Why we should celebrate (and not fear) quantum computing
By Bob Sutor, vice-president, AI, blockchain and quantum solutions, IBM Research
Electronics Regulations & Standards Engineering Supply Chain Quantum Computing quantum computing quantum research quantum research Quantum system Quantum systemOver the past year, various headlines have warned ominously about the impending threat of quantum computing to encryption and security. As a scientist and executive for the leading corporate program of quantum research, I can assert these fears are unnecessary. We are still decades away from breaking modern encryption with this technology, when it won’t matter anyway, for reasons I’ll explain.
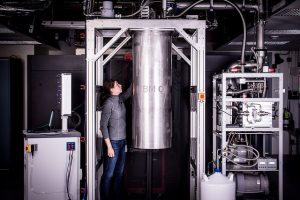
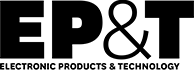
Figure 1: IBM Research builds its most powerful universal quantum computing processors.
Photo credits: IBM Research
More importantly, this preoccupation distracts us from what we should really be thinking about: how quantum computing will accelerate human discovery and benefit our lives. Rather than fear quantum advances, we should celebrate them.
The power of quantum computing lies in its unique properties. It exploits the laws of quantum physics to perform operations on data that go well beyond the capacity of the binary digits, or bits, upon which today’s computers are based.
Qubits exhibit states known as superposition, entanglement, and quantum interference
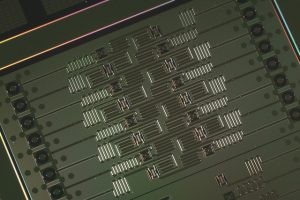
Figure 2: IBM 16 Qubit Processor
Quantum systems do this by using extraordinarily delicate quantum bits, or qubits, which are extremely difficult to manufacture and keep stable. These qubits exhibit states known as superposition, entanglement, and quantum interference. By manipulating them we can massively increase our ability to compute. We believe it will take a system with at least 50 qubits to begin handling certain problems that no classical computer can ever solve on its own, no matter how large.
Modern encryption is based on the premise that the factoring of numbers required to break encoded information is nearly impossible to do with current systems. In fact, it would take many thousands of years even for the most powerful supercomputers to figure out. However, in 1994 MIT mathematician Peter Shor developed his famous quantum algorithm demonstrating that factoring would be exponentially faster on a quantum computer.
Figure 3: Input microwave lines
But here’s the catch: factoring the kinds of numbers used for encryption on a quantum computer will require tens of millions of qubits that achieve fault tolerance. That’s tens of millions more physical qubits of higher quality than we have in quantum computers today. Systems like this are many years away and will require advances in physics, mathematics, and engineering.
Powerful universal quantum computing processor contains 17 qubit
To put this into perspective, earlier this year IBM successfully built and tested its most powerful universal quantum computing processor, which contains 17 qubits. It will serve as the core prototype processor for IBM Q, an industry-first initiative to build commercially available universal quantum computing systems.
With this foundation, we anticipate scaling future processors to include 50 or more qubits within the next few years. We continue to make many advances toward this goal. But neither we nor anyone else in the industry are anywhere close to posing a threat to encryption. By that time, researchers will have discovered new encryption protocols that are either “quantum proof” or that leverage quantum mechanics for even higher levels of security. This work is already underway.
What is far more exciting to us are the many benefits early quantum computers are expected to provide to society in just the next few years. In that time, we anticipate the discovery of new algorithms that can run on these systems that untangle the complexity of molecular and chemical interactions, address complex optimization problems, and make artificial intelligence much more powerful. Such advances could open the door to new scientific discoveries, life-saving drugs, and huge improvements in supply chains, logistics and the modelling of financial data.
This is a pivotal time for quantum research, when we should focus our energies on the true promise of this emerging technology, and not imagined threats. The truth is we are on the verge of a new age of human discovery with quantum computing. And that is something worth celebrating.
